Howdy, Stranger!
It looks like you're new here. If you want to get involved, click one of these buttons!
Categories
In this Discussion
Guests: Kayla Adams * Sophia Beall * Daisy Bell * Hope Carpenter * Dimitrios Chavouzis * Esha Chekuri * Tucker Craig * Alec Fisher * Abigail Floyd * Thomas Forman * Emily Fuesler * Luke Greenwood * Jose Guaraco * Angelina Gurrola * Chandler Guzman * Max Li * Dede Louis * Caroline Macaulay * Natasha Mandi * Joseph Masters * Madeleine Page * Mahira Raihan * Emily Redler * Samuel Slattery * Lucy Smith * Tim Smith * Danielle Takahashi * Jarman Taylor * Alto Tutar * Savanna Vest * Ariana Wasret * Kristin Wong * Helen Yang * Katherine Yang * Renee Ye * Kris Yuan * Mei Zhang
Code Critique / Book Review: Travesty Generator by Lillian-Yvonne Bertram
Hello,
I have recently read Lillian-Yvonne Bertram's excellent new book of poetry, Travesty Generator. I started writing a short book review for CCSWG, but I just kept digging into it. So what follows is my hastily-written and barely-edited analysis of three of its poems. I'm interested in discussing this book and in whatever conversation my analysis/review may lead to here, but I mainly want to post this because I think this community will dig this book too and I wanted to make sure more people know about it.
What follows is pretty rough, so I will probably copyedit and refine it somewhat after posting.
Lillian Yvonne-Bertram's book of poetry is titled Travesty Generator (Noemi Press, 2019) in reference to Hugh Kenner and Joseph O'Rourke's Pascal program to "fabricate pseudo-text" by producing text such that each n-length string of characters in the output occurs at the same frequency as in the source text. By combining different authors through this algorithm, one might stumble across a travesty of "haunting plausibility" wherein James Joyce's writing becomes muddled with Henry James'. The pseudo-text's nonsensibility is simultaneously its transgression and its literary possibility, but for Kenner and O'Rourke and the many progeny of their program, those possibilities extend no farther than a formal curiosity or at best an insight into an author's poetic style.
When Charles O. Hartmann uses Travesty in his Virtual Muse, he finds that the nonsense it generates helps Hartmann's composition process by disrupting the habits he found himself following as a writer. Of the generator itself, Hartmann noted with some awe that "here is language creating itself out of nothing, out of mere statistical noise" (63).
What Bertram accomplishes in naming her book after travesty generator is to raise the stakes in computer-generated poetry. Whereas for Kenner and O'Rourke, labeling their work a "travesty" is a hyperbolic tease, a literary burlesque, for Bertram, the word is reinvigorated with a feeling of its political reality. In 2013, attorney Don West, responding to the not guilty verdict for his client George Zimmerman in the shooting death of Trayvon Martin, congratulated the jury for keeping "this tragedy from becoming a travesty." West is implying that the media attention on the case risked creating what he and Zimmerman would have called a farcical miscarriage of justice for his client.
"Counternarratives"
For others, the event was always a travesty: a "grotesque parody or imitation" of criminal justice enacted by a civilian playing at being a law enforcement officer that resulted in an extra judicial killing of an unarmed high-school student.
Central to anyone's response to that verdict is how one understand the narrative of events on February 26, 2012. This is question Bertam takes up in her poem "Counternarratives" which presents sentences, fragments, and ellipses that begin ambiguously but quickly resolve into a series of hints, implications, and images around Trayvon Martin's killing. These narratives are "counter" for several reasons, most importantly for the fact that they include Martin's point of view:
He never told anyone, but he always wanted to go to space camp.
...
He rides from station to station until he can rest at home.
...
Sometimes he wakes feeling gone and doesn't know why.
Bertram prints these sentences with others in 14 successive stanzas, each printed on its own face of a page, each growing in size until the blank 13th stanza breaks the pattern. One can see the inertia of automation and the inevitability of processes at work in the consistency of this pattern and in the way the poem intersects other perspectives that include the algorithmic prompts of search engines ("People also ask: what really happened?") and the horticultural ("Only the flowering catalpa trees are on watch") -- all echoes of the machinic "generator" in the book's title. But because this is literally generated from computer code, these observable processes yield two other significant "counters" at work.
Bertram does not share the source code for this poem, but in an appendix acknowledges that it is adapted from the Python version of Nick Montfort's poem, "Through The Park," published in his 2014 collection #! and available on his website. Montfort's poem is framed by a for loop, or a "counter," i, iterating through 8 sequences, each of which prints a numbered stanza:
for i in range(8):
For each loop and each stanza, the program selects a number 7 - 11 (phrases = 7 + random.randint(0,4)) and randomly deletes lines from the initial 25 unti the lines that remain reach the selected number of phrases, joining those remaining lines with ellipses. The resulting poems achieve their meaning through omission, elision, and innuendo, relying on the ambiguity of language and the way readers respond to that ambiguity by imagining the context that creates the poem's implied narrative. What that narrative is will depend on which lines end up being printed, and in #!, the 8 stanzas that Montfort selects show how widely those contexts may diverge, and these could range from a casually flirtatious encounter with a stranger to a sexual assault. The latter reading is activated by whether two or three key phrases are chosen to remain in the resulting poem. The suggestive phrases "The girl puts on a slutty dress", "The man makes a fist behind his back," "The man's breathing quickens," and "The man dashes, leaving pretense behind" makes "The girl's bag lies open" metonymic and lets the question of what their glances know "The man and girl exchange a knowing glance" hinge the meaning of the moment toward violence.
The girl puts on a slutty dress. ... A wolf whistle sounds. ... The muscular man paces the girl. ... A wildflower nods, tightly gripped. ... Laughter booms. ... A lamp above fails to come on. ... The girl's bag lies open. ... A patrol car's siren chirps. ...
This violence is implied, but generic, and the poem's meaning is about the way language gives shape to violence. The victim blaming in the "slutty dress" line, for example, is Montfort reminding us of the ways that words create an inertia of belief that precedes knowing. Ultimately, however, this is all that is stake for the poem.
Bertram's "Counternarratives" is more than an adaptation of Montfort's because it is also a counter to "Through the Park." Whereas the context for Montfort's poem is hypothetical, Bertram's is real and specific. While we cannot consult Bertam's source code, it is possible to imagine the process whereby Montfort's "A wildflower nods, tightly gripped" becomes Bertram's "The frangipani swans in the moonlight" and Montfort's "She puts on a slutty dress" becomes "People also ask what he was wearing." or perhaps "No mention of his clothing."
What Trayvon Martin wore -- a hoodie -- became a symbol for that event and a meme for Black Lives Matter because of its power in calling out racial profiling. The assumption that a "black man with a hoodie" is inherently threatening is conveyed in Bertram's "People also ask..." phrasing, which quotes a google search suggestion. In the context created by this poem, this question recalls the victim blaming in Montfort's poem's "slutty dress" line, but following Bertram's move from the generic to the particular, this search suggestion and other's like it are drawn from reality.
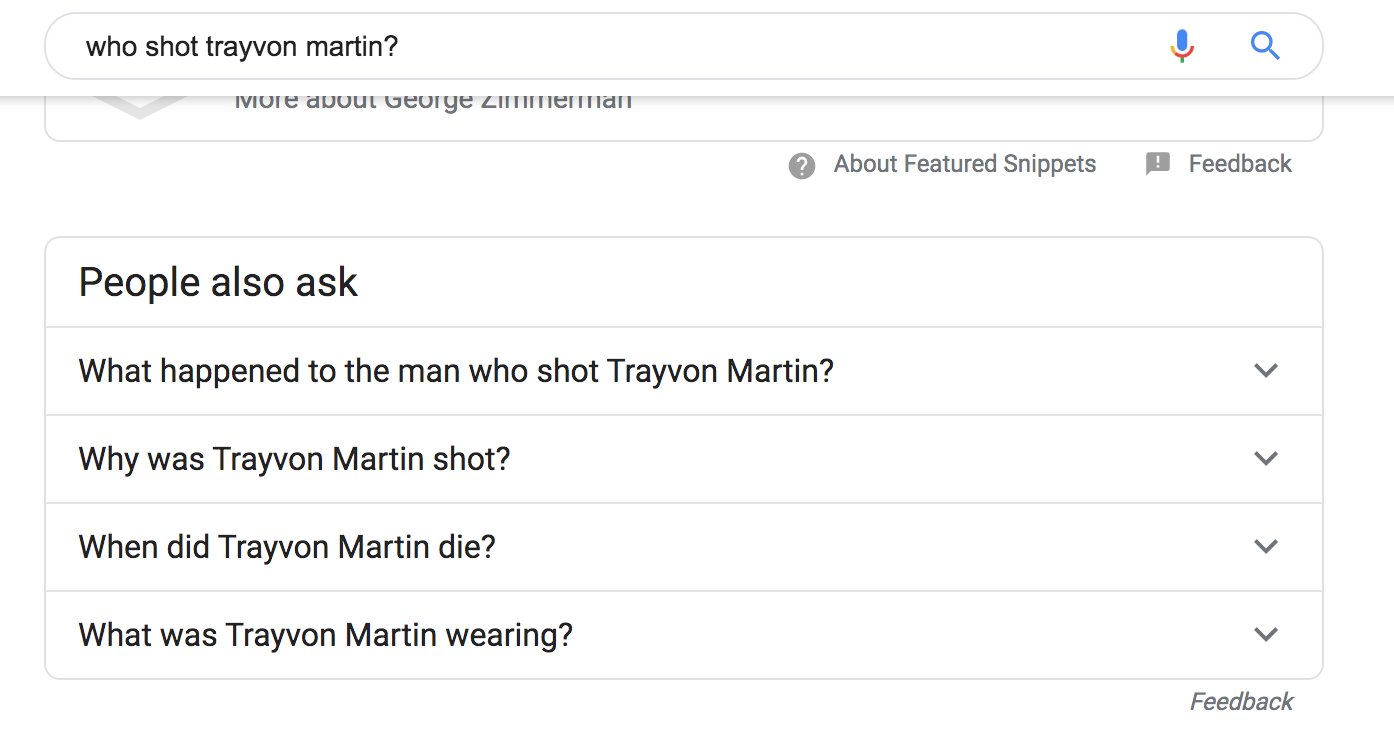
After a few trials, I discovered the suggestion "What was Trayvon Martin wearing?" in response to the search query "Who shot Trayvon Martin?". I also found another recurring line, and the final line in Bertram's poem, "People also search for: Emmett Till" come up in several similar searches. This is a demonstration of the way that search engines, like language, become the machinery for racial violence through their operationalization of algorithmic bias. Notably, Bertram's line does substitute Martin's name for the pronoun "he," so the antecedent could be Zimmerman, especially since neither are named outright in the poem. This final opening out of meaning is another significant way in which the poem reflects on its constructedness.
In the book's appendix, Bertram notes that the output of her program has been edited and arranged, and this rewriting is evident in the way that certain of the phrases evolve as the poem progresses. In some cases, this is an evolution that follows a trajectory implied to begin in Montfort's version which has its possible final line, "A patrol car's siren chirps."
Bertram's lines (never the last for any of her 14 stanzas) proceeds from there to
[3] ... A patrol car's siren sings several streets away...
[10] ... Several weeks away, a patrol siren sings...
[11] ... A patrol car's siren sings several streets way...
[12] ... A patrol car's siren swats bugs and halos away...
[14] ... A siren signs
several streets away.
The most striking movement in the poem is that way that "Counternarratives" uses ellipses. Whereas Montfort's poem is suggestive through the innuendo created by stochastic omission, Bertram's is subversive through the implications of its elisions, and those elisions and ellipses gradually resolve into prosodic syntax as the text of the poem gradually takes up its poetic mechanism. The phrase that first appears in stanza 4 as "Real gaps spread in the tropic of paradise" is stark in its proximity with its initial following line "Forty-two miles from Disney," where proximity here is both the poetic associations as well as the geopolitical identity of this Orlando suburb.
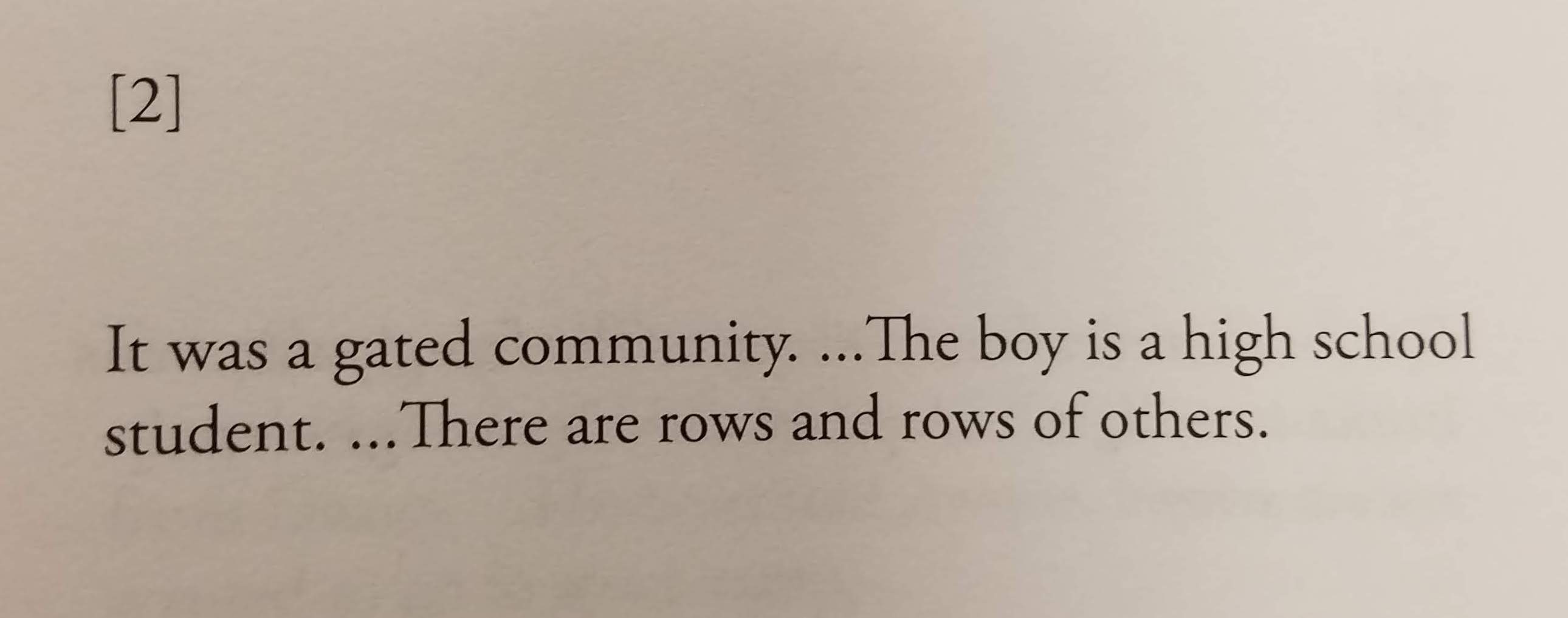
After the blank penultimate stanza -- a final elision -- this line has become "Gaps split open the tropic of paradise." A blank line splits the "siren signs" sentence, followed by the now damningly unambiguous "Cause of death: It was a gated community."
By editing and arranging the output of her program, Bertram is declining to let the machinery of language or Python control the narrative and opening up paths to resistance by insisting that we bear witness to the tragedy without retreating to the algorithmic distance of a travesty.
Two other poems in Travesty Generator offer similar insights on the relationship between the mechanization of computing and use those processes to interrogate the structures that make them possible.
"three_last_words"
The poem that opens the book, "three_last_words", is at a functional level a restatement of the program in Nick Montfort's "I AM THAT I AM", which is itself a version or adaptation of Brion Gysin's permutation poem of the same title. That phrase does not appear in Montfort's version. Rather, Montfort's program defines a permutations function and then executes that function with the string 'AEIOU' as its argument, yielding the 120 possible rearrangments of AEIOU as its outcome. Montfort's code accomplishes this succinctly through an elegant recursion as the permutations generator works through a list of elements, rearranging all of the following elements (elements[1:]) by passing them back into no more next elements remain.
"I AM THAT I AM" (from Montfort)
def permutations(elements):
if len(elements) == 0:
yield elements
else:
for result in permutations(elements[1:]):
for i in range(len(elements)):
yield result[:i] + elements[0:1] + result[i:]
Bertram's generator is mostly the same, code but the commentary she adds -- and more importantly the uses she puts it to -- changes the meaning entirely. That new meaning is jarring and, as in "Counternarratives," tragic.
Bertram alternates lines of code with comments that accumulate toward something unavoidable:
"three_last_words" (excerpt) (Bertram)
def permutations(elements):
#the
if len(elements) == 0:
#the knife
yield elements
#the knife they
else:
#the knife they hung
Eventually the completed sentences warns, "#the knife they hung him on / #was a legal trinket". When he was killed by Daniel Pantaleo while being placed under arrest, Eric Garner was selling loose cigarettes -- a minor violation of cigarette tax law. So "legal trinket" here brings to mind the way that Garner's alleged crime of selling cigarettes became a dog whistle for racist backlash to Black Lives Matter -- responses that included an Indiana police officer selling t-shirts with the mocking slogan, "Breathe easy, don't break the law." So a "trinket" because the relatively trivial infraction apparently justifies police violence.
"Trinket" does something else here as well, by naming a service, Trinket.io, which allows users to create snippets of Python code that they can embed and run in a webpage. This apparent reference hints at the practical environment for running this code, something that is unnecessary for Montfort's ontological poem because of its tautological symmetry.
Bertram's poem instead invites us to experience the consequences of her program with an explicit invitation a page later to
#run the code
#in this cell
#away
The "cell" here may connote a jail cell, but more practically it describes a Python Notebook cell. Python Notebooks are a common way to experiment with Python, and the samples of output and the poem's culminating error message are typographically consistent with with what one would see while running this code in a notebook.
Montfort's program runs one permutation and prints the output: 120 variations on the five vowels arranged from 'AEIOU' to 'UOIEA' in 8 tidy, monospaced columns.
Bertram's program runs three times, and whereas Montfort's final line of Python 2 code prints the permutated combinations as a string (print ''.join(list(permutations('AEIOU')))), Bertram's Python 3 simply prints the list as it is represented in Python's memory. The first iteration permutes a single-character:
print (list(permutations("I")))
['I']
In addition to this invitation to experience the practical implementation of the program, this different in printing the yield of the permutations function pulls us toward the subjective point-of-view of the Python runtime that experiences the code, and the chaotic typography of the output -- in contrast to Montfort's neat rows and columns -- performs the messy complications of computation that will eventually culminate in the runtime's demise.
There is one more subtle variation between Montfort and Bertram's code in the final line of the constructor. As it iterates through the elements list (a string of text characters, in this case) the newly-permutated line yields with + result[i:] for Montfort or + result for Bertram.
The functional difference is that Montfort's line restores to the target string only those parts of the input string that come after the character operating for the current iteration. The [i:] slice captures only those elements after i. Bertram's version retains and concatenates the entire working result, so the practical difference is that while Bertram's code will generate the same number of permutations, the strings it generates gradually become longer. The last element in the permutations of the string "can't" is "t'nact'nat'nt't". I see this introducing a measure of inexhaustibility. Whereas the 120 permutations of "AEIOU" are a complete and homogenous set, permutations("can't") is asymmetrical and growing. The articulation of print (list(permutations("breathe"))) runs past the right and bottom edges of the page.
The asymmetry culminates finally and dramatically with the full phrase "I can't breathe". Bertram's code concludes with the printout out of a Python MemoryError because the number of possible combinations of the 15 letters in that phrase (1,307,674,368,000) exceeds the available memory on the computer hosting the Python runtime, and like the 15 seconds that Officer Pantaleo held Eric Garner in a chokehold, those 15 characters result in the death of the Python Notebook or the computer hosting it.
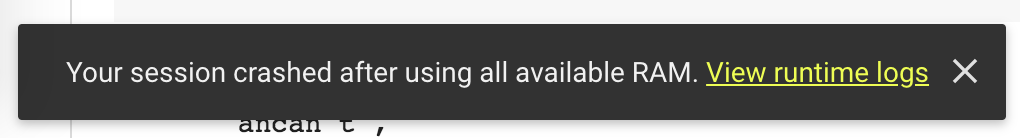
I attempted to run Bertram's code two different ways: first in a Google-hosted Colab Notebook and later in a Jupyter Notebook running on my laptop. The Colab Notebook ran for some time with the RAM usage indicator creeping slowly to the right and becoming first green, then yellow, and finally orange before the runtime crashed and disconnected.
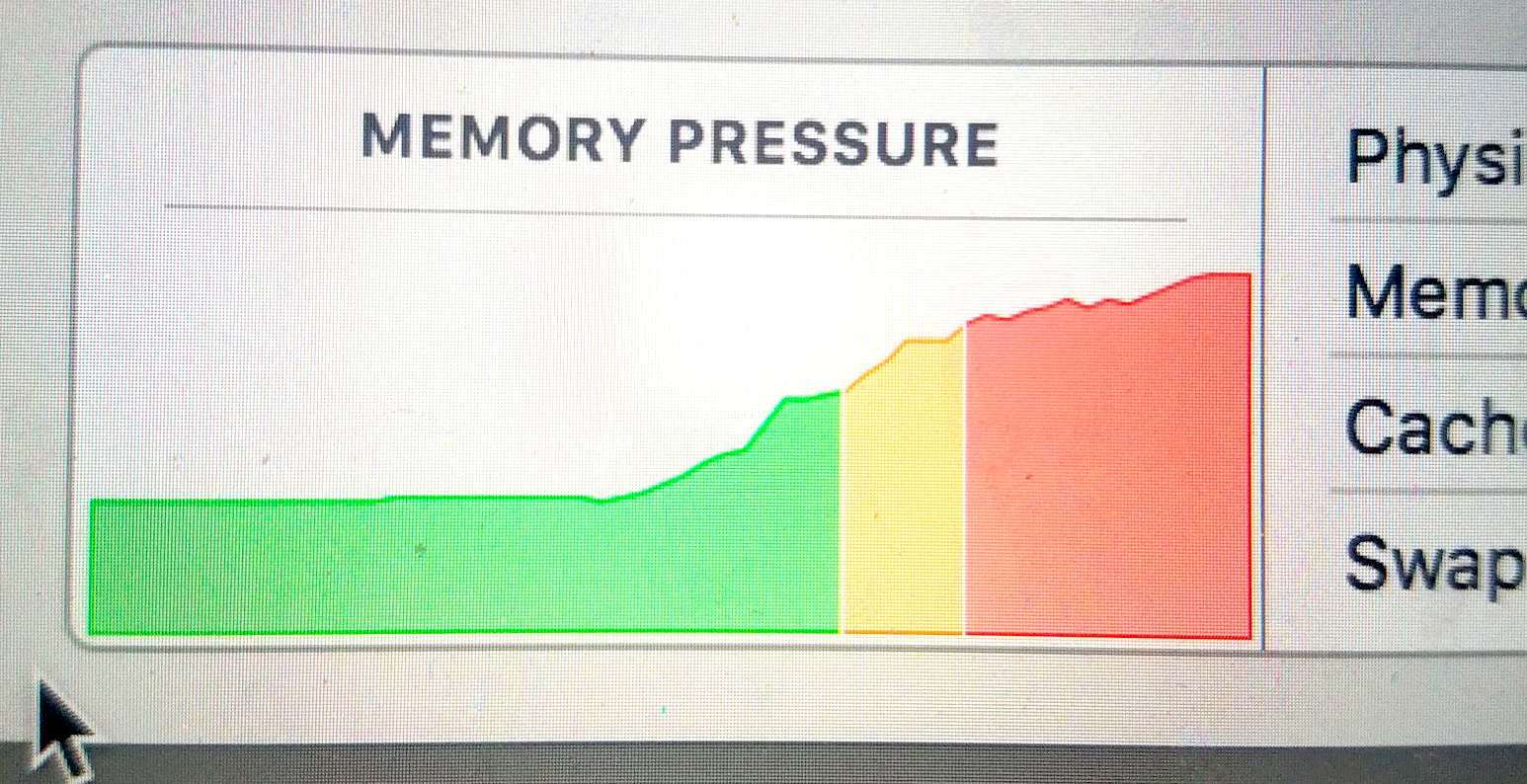
On my Macbook Pro, the results were similar, but as Python continued to take up more and more RAM, my computer gradually stopped working. The cursor slowed down, the trackpad clicked more slowly, and keyboard shortcuts stopped working. I couldn't take a screenshot, so I had to use another device -- my phone -- to capture the final moments before I resorted to a hard reboot and power cycle.
It seems trivial or maudlin to compare a computer running out of memory to the tragedy of Eric Garner's asphyxiation and death, but the way the computer's memory usage creeped steadily upward conveyed a vivid anxiety and sense of panic in a way that was hauntingly effective. This poem is directly addressing the physical environment of computing in a manner reminiscent to Montfort's poem "Round", or Sam Lavigne's parodic "Slow Hot Computer" project that "makes your computer run slow, and hot, so you can be less productive" by running "processor-intensive calculations" in a web browser.
This kind of metaleptical irruption of attention -- what Terry Harpold has called "recapture" -- is typically accomplished in the service of play, both in the satiric sense of Lavigne's playfully critical projects and, for Harpold, in both the literal sense of playing videogames and the semiotic sense of expressive freedom within constraints. In Montfort's examples, recapture moderates the conflicts of entanglement with technical limitations are expressed through the terms of the gameworld, as when a text-based game attempts to parse an unknown word of user input and it replies "I didn't quite understand that" instead of reporting an error code or just crashing. Recapture is fundamental operation of videogame, which means that "recapture happens during play, in the complex digressions and feedback loops that are activated in actual play."
Bertram's works withe same entanglement of technical process and expressive semiotics, but poetry is not a videogame, and in this case, the poem denies its reader the recapture of memory, challenging us instead to bear witness to the trauma it represents.
As Wendy Hui Kyong Chun has discussed, computer memory is an "enduring ephemeral," always-already conflating memory with storage and, through metaphors and pretenses of permanence. She notes that the instability of this term, memory, follows the volatility of RAM, which is "based on flip-flop circuits and transistors and capacitors" and which require a steady electrical current" (169). Like human memory, software "memory is not a static but rather an active process. A memory must be held in order to keep it from moving" (167). Bertram's software presents the volatility of memory as the entanglement of poetic representation, police brutality, and technical limitation, and by setting it up to fail, Bertram invites us to reenact the trauma of that brutality and interpret its technical and political consequences.
When Bertram disrupts the symmetry of Montfort's slices (result[:i] and result[i:] becomes result[:i] and result so that "ehtaerb" potentially becomes the drawn-out, Joycean susurration "ehtaerbehtaerehtaeehtaehtehe", that is, print(list(permutations("breathe"))[-1])), but both versions of the generator choke on Eric Garner's three last words. Memory fails, but the poem preserves its failure even as its overflow suggests a world uncontemplated by code. This overflow is not infinite -- hinting that someday, when it becomes possible to run this program with the multiple terrabytes of RAM necessary to compute and convey one trillion three-hundred seven billion six-hundred seventy-four million three-hundred sixty-eight thousand lines, the program will complete, but until then we are compelled to follow Bertram's invitation to bear witness and
#return
#this articulation
#the exhaustion
#we can't stop hearing
A NEW SERMON ON THE WARPLAND
Like "three_last_words" and "Counternarratives," "A NEW SERMON ON THE WARPLAND: a poem by algorithm" is a work with a genealogy, and Bertram directs us to the source codes that ground it. This is another poem where Bertram gives credit to an example by Nick Montfort, but his code is a straightforward implementation of Alison Knowles' "A House of Dust," so Knowles is the more appropriate counterpoint for Bertram's work. More significantly, Bertram acknowledges "that some words and phrases ... are taken directly from Gwendolyn Brooks' corpus" in her notes, so understanding those origins allows these phrases to act hypertextually as a bridge into Brooks' poems. Bertram encourages us to explore that bridge by recommending Brooks' 1987 collection Blacks, and specifically points to "The Sermon on the Warpland" and In the Mecca as especially important sources. ("Boy Breaking Glass" and "THE WALL" also seem to be the sources for several phrases.)
Alison Knowles and James Tenney produced "A House of Dust" in 1968, the same year that Gwendolyn Brooks published In the Mecca. The source code for "House of Dust" is not publicly available, but its function is easy to deduce by examining the output published in three different venues. Knowles created the structure and four lists of words and phrases, and Tenney wrote those into FORTRAN code that creates quatrains by selecting and printing one item from each list, indenting each line a few spaces before returning to left justification as each new quatrain begins.
A HOUSE OF ROOTS
AMONG HIGH MOUNTAINS
USING NATURAL LIGHT
INHABITED BY VARIOUS BIRDS AND FISHES
A HOUSE OF WOOD
BY A RIVER
USING ALL AVAILABLE LIGHTING
INHABITED BY HORSES AND BIRDS
A HOUSE OF DISCARDED CLOTHING
UNDERWATER
USING ELECTRICITY
INHABITED BY FRENCH AND GERMAN SPEAKING PEOPLE
When I created a simulation of this poem in Javascript, I named these lists materials, places, lights and inhabitants. Montfort used the names material, location, light_source and inhabitants.
Bertram doesn't share her code in Travesty Generator, but observing its patterns reveals it to have a similar structure of lists randomly sampled. Also, two earlier versions of Bertram's "A NEW SERMON ON THE WARPLAND" are available online, one in Javascript (https://ruby-buffet.glitch.me) and another in Python 2 (https://www.lybetc.tech/new-sermon-code). In the Javascript version, each list simply bears a number (one,two, etc.), but the Python 2 version assigns names that signpost the function of each list. There are differences between the source code shared on Bertram's website and the code that created the poem published in Travesty Generator, but the five names suggest their content and reveal Bertram's primary departure from Knowles: materials, locations, verb, means, and outcome.
A NATION OF GRIEF
IN THE CUT
SUMMONING
ANY MEANS NECESSARY
TO REFUSE ERASURE BY ALGORITHM
A NATION OF OLD DISPOSSESSIONS
STILL FIGHTING
CONJURING
ANY MEANS NECESSARY
TO REVISE ERASURE BY ALGORITHM
Comparing "House of Dust" with "NEW SERMON" reveals more differences than the addition of a fifth line. Knowles' locations are diverse but more stable -- "BY THE SEA", "IN MICHIGAN", "IN A HOT CLIMATE", "ON AN ISLAND","IN SOUTHERN FRANCE","AMONG OTHER HOUSE" -- while Bertram's are active, violent, or disrupted, and some are not conventionally "locations" but moreso describe liminal states of being:
...IN THE CUT...
...STILL FIGHTING...
...IN FRONT OF A WINDOW ABOUT TO BE BROKEN...
...IN TRANSLATION...
...BETWEEN SCYLLA AND CHARYBDIS...
...IN THE SHIP'S HOLD...
Instead of a house, Bertram addresses her sermon to a "NATION". Allusions to the slave trade are perhaps most striking in comparing the subtle differences in phrases between Knowles' "ON THE SEA" and Bertram's "ON SHIPS", but the shifts in Bertram's poem is much more than a inversion of Knowles'. While "A House of Dust" dwells, a NEW SERMON moves, acts, and resists. The verbs and means lists propel each cinquain through the same means -- "ANY MEANS NECESSARY" -- to the same outcome: TO REFUSE ERASURE BY THE ALGORITHM.
The earlier Python 2 version includes multiple possible outcomes, but the verbs list is somewhat shorter. Because the printed version of the poem includes the same outcome in each cinquain, it is reasonable to infer that its source code is closer to the Javascript version where list five only contains one element, to refuse erasure by the algorithm. The means list works the same way, demonstrating that the only option is Malcom X's ANY MEANS NECESSARY.
For both of these one-choice lists, the program is still selecting that choice as the result of a process. The Python 2 draft uses the common random.choice() function, and the Javascript version takes a custom function with a comment remarking on its conventionality:
// This is a very common randomizing function.
// It takes a list (array) and returns one at random.
function select_random(x){
y = x[Math.floor(Math.random()*x.length)];
return y;
}
The fact that this program is making a choice with no freedom plays into the slavery imagery within the poem, but revisiting "A House of Dust" opens another way of understanding the significance of this choice without a choice.
Benjamin Buchloh argues that Knowle's project in creating "House" was to find a way to deconstruct the "prison house of language". Noting the irony of an avante-garde artist like Knowles using a house, that most conventional vehicle for subject formation, as her central figure, Buchloh contends that the aleatory construction method of the poem demonstrates the infinite fluidity of the process of subject formation.
Channeling Nietzsche, Buchloh goes on to observe that the constructedness of "House of Dust" resists the subject's being at "home" in language. "Knowles's The House of Dust conceives of the process of subject formation as a perpetual process of construction and undoing, precisely to prevent it from becoming an inhabitant of the prisonhouse of language, a merely substitutional system of fraudulent and agressive convictions...the formation of of the subject at this point in history has become a more complex and, by necessity, a more open process, since the subject's intersections with language...are certainly no longer the primary ... foundations". Buchloh's "convictions" are a play on words, a synonym for "belief" in the mode of the metaphoric correctional system. But it also opens up another angle on "NEW SERMON," which is filled with punishment and captivity but conspicuously without conviction.
Although the Javascript version of the poem does include "of parolees" and "of prisoners" as possible materials, possibly drawn from Brooks' "The Wall", the printed poem's materials and locations invoke punishment without the framework of judicial justification:
...A NATION OF SPECIFIC CHAINS...
...IN THE SHIP'S HOLD...
...A NATION OF MEDGAR EVERS...
...IN A STRING-DRAWN BAG...
In this way, Bertram's poem comes back to the prison house of language that Knowles' is playfully resisting. Captivity and imprisonment are not just metonymic critiques for the post-structuralist decentering of lexical epistemology; instead, the prison house of NEW SERMON is the literal kidnapping, enslavement, and genocide of Africans whose exploitation built the foundations of this nation.
Finally, by naming one of the lists verbs, Bertram follows a schema one often finds in generative works that use context-free grammar: patterns or templates where words are given a syntactical place based on their part of speech. In NEW SERMON, the verbs list does the most work to take the poem away from its origins in "House of Dust". The seven verbs that appear in the 22 printed cinquains all suggest movement with resistance or a sense of bring something out from below:
DIGGING UP
SUMMONING
CONJURING
DIVINING
UNEARTHING
STRIKING MATCHES AGAINST
HOLLERING DOWN
Each of these verbs immediately precedes "ANY MEANS NECESSARY". So, by omitting the preposition "by" from Malcom X's well-known phrase, the call to action in the poem asks its reader to dig up, to unearth, strike matches against their own means of refusing erasure.
In an appendix on the book, Bertram quotes Harryette Mullen's essay "Imagining the Unimagined Reader," "When I read words never meant for me, anyone like me ... then I feel simultaneously my exclusion and my inclusion as a literate black women, the unimagined reader of the text." Bertram likewise considers herself an "unimagined coder."
I use codes and algorithms in an attempt to create work that reconfigures and challenges oppressive narratives for Black people and to imagine new ones. I consider this an intervention into a set of literary practices that have historically excluded women and minorities.
For each of the works I have analyzed here and for many others of 10 poems in Travesty Generator, Bertram uses the generators of computer-generated poetry to critique, resist, and replace narratives of oppression and to make explicit and specific what is elsewhere algorithmically insidious and ambivalent.
Lillian-Yvonne Bertram's Travesty Generator is a challenging, haunting, and important achievement of code poetry.
Comments
Wow, @zachwhalen, what an amazing piece.
I found it interesting to see the way Cathy Park Hong's quote on the collection's website frames the piece:
It's been a bit of a tradition with the books by @nickm to publish the source code along side the sample output. Is @nickm by implication in a position of privilege to share his code? I usually see that choice as part of Nick's larger project, to put his code forward _as _the poems, or the output of his poetic practice. So thinking about it, this quote from Hong suggests that Bertram has done something transgressive by hacking this code -- and I see this point -- but it doesn't feel like @nickm is the target of Bertram's counternarrative. How does not publishing the source code affect the meaning of these poems that are the "hacked" version of code by white men?
Have you asked Bertram for the source code? Or would asking that be an intrusion?
Also, I had a question about the ellisions. Can you show us what that looks like in the text beside @nickm's? I'm afraid I don't have a copy of Bertram's book?
Thank you @zachwhalen for this post. You assembled a lot of ideas (Buchloh!) and a couple of points have stood out to me, for specific reasons:
Zach Whalen quoting Wendy Hui Kyong Chun:
A memory must be held in order to keep it from moving"
It was devastating to read this exact line just hours after learning that Zimmerman has, as of today, filed a $265 million defamation lawsuit against Senator Elizabeth Warren and Pete Buttigieg. Zimmerman is claiming that the two candidates referenced Zimmerman in "defamatory tweets" to expand their acceptance among voters of color. Upon reading this I thought about how to keeping a memory 'alive' has unfixed dimensions. For the Martin family, this is re-traumatization. Not only have they lost their child, their brother, their cousin, now they must bear witness to their beloved becoming a political pawn. Again. A memory must be held in order to keep it moving...
I'm over-examining the word 'held', because I often use that word to mean 'image'; to mean to hold something close to thought, as a mental talisman for awareness, for consolidating purpose or focus at any given time. To hold a memory is to give shape to an impression, an image. And images are never static (not even cibachromes).
Zach Whalen quoting Cathy park Hong:
...how black experience becomes codified, homogenized, and branded for capitalist dissemination.
I agree with this analysis, very much. After Trayvon Martin, after Eric Garner, after Ferguson, after Diamond Reynolds, there were several media and digital scholars publishing online think pieces about "Stop watching Black death" and "stop circulating Black death." I agree that non-white bodies don't exist to be spectacles, during life or after being murdered. And I absolutely agree that our 24 hour news infoscape, white owned, is extremely exploitative and profits exponentially off of tragedy/spectacle/injustice by commodifying it.
And yet, I kept asking myself: to those who kept promoting the idea of "not circulating black death", didn't they ever think to use their clicking power differently? As in, if you see another article about racialized injustice, why are you clicking on a Washington Post link, or a New York Times tweet, when you could be clicking on Ebony, or Jet, or Blavity? Why not think more critically about directing one's clicks? I'm not saying people should run and go look at the spectacle of suffering of people of color, but when one wants to read about events, we do have a choice, and so we should click wisely. We should click as close to the affected communities as possible in order to gain understanding from those who know specific circumstances. Not another flown-in outsider reporting on a zipcode they have never been attuned to.
In the perverse ways that infoscapes are subsidized (ads, clicks, eyeballs=$), is unsophisticated to think that avoiding to click on white-owned media is viable digital resistance?
Sidenote: In 2014 and onward, Teen Vogue under the direction of Elayne Welteroth published award-winning in-depth coverage of racism in America in a direct manner that did not commodify current or historical brutality, but used current events as springboards for education—educating young girls to aspire to be more of themselves, politically and personally. But those accolades didn't save the the print title from going out of business.
All that to say that i strongly believe that the social memories that shape our time, our relations, our social systems, are to be held far more responsibly than we are taught to. But we can choose who we learn from—can directing our clicking power be a form of transformative digital justice?
@markcmarino Thanks for this response and for the opportunity to keep the conversation going this week!
You raise a really important question here:
Bertram discusses her identity as an "unimagined coder" or programmer in an afterword, which I think is mainly what Cathy Park Hong is noticing. So I think Bertram's target is more the ubiquitous milieu of programming (with its history of tending to exclude or oppress women and minorities disproportionately) than @nickm specifically. At any rate, she thanks Nick for his guidance and support in the acknowledgements, even though my reading of "Counternarratives" is that, at one level, it critiques "Through The Park."
Lillian-Yvonne does include source code for two of the poems -- "three_last_words" and "@Tubman's_Rock" -- but I think her inclusion of these sources accomplishes a different purpose than @nickm sharing his. Nick Montfort's "I AM THAT I AM" is offered without commentary or justification. John Cayley calls this poem "deterministic, the generator of a specific artifact, in this case a minimalist tour de force of, at one and the same time, self-reflective formalism and high literary allusion.". In that review, Cayley is interested in whether the code is the text (if it is the text), and what I think he's saying here is that this poem is formally self-contained. If we get the allusion to Brion Gysin's permutations, we may view first view the output as the evidence of that allusion, and then admire the elegance of Montfort's minimalist programming. At least in this case, I get the sense that he shares the code because the code is the poem.
In Bertram's case, for "Counternarratives" and others, the technical problem of permutation has already been "solved" so what's meaningful is the use she puts it to. "three_last_words" includes commented lines that create context and steer our response. And "@Tubman's_Rock" -- which is based on Balestrini's Tape Mark 1 -- includes quite a few comments that acknowledge sources and explain some of the references included in the potential poems, which we get 11 of in the pages of Travesty Generator.
And whereas in #!, the code precedes the text, "three_last_words" prints the code in a way that simulates the process of running it iteratively in a notebook, and it functions more like a footnote or bibliography to "@Tubman's_Rock," which is another example of its different purposes here.
@markcmarino wrote:
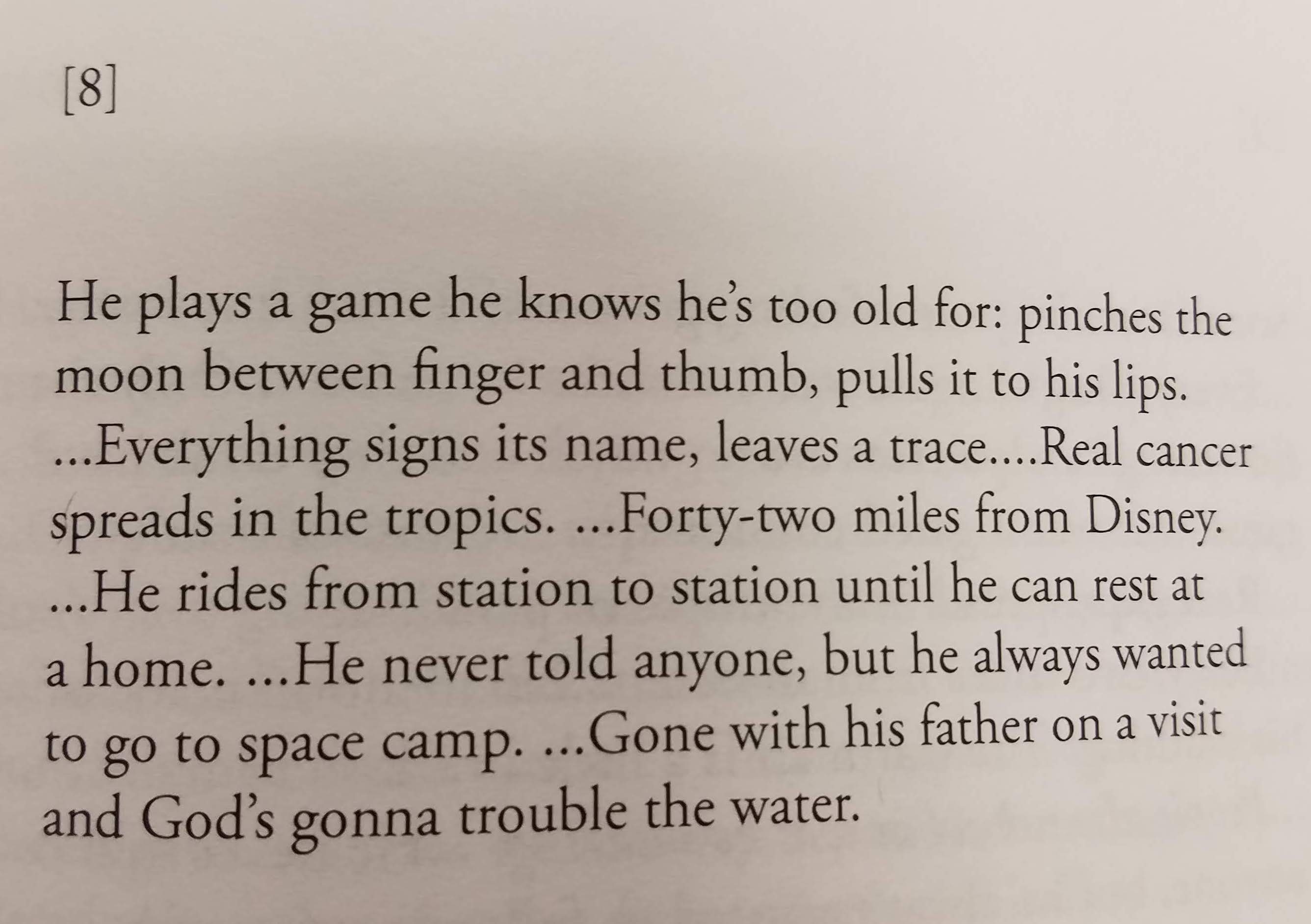
Sure, it's kind of hard to describe, so here are a few examples. (Apologies for posting images of text -- I will transcribe later).
First, a sample stanza from @nickm's "Through the Park":
And then a few from "Counternarratives," which gradually increases the number of fragments and decreases the ellipses:
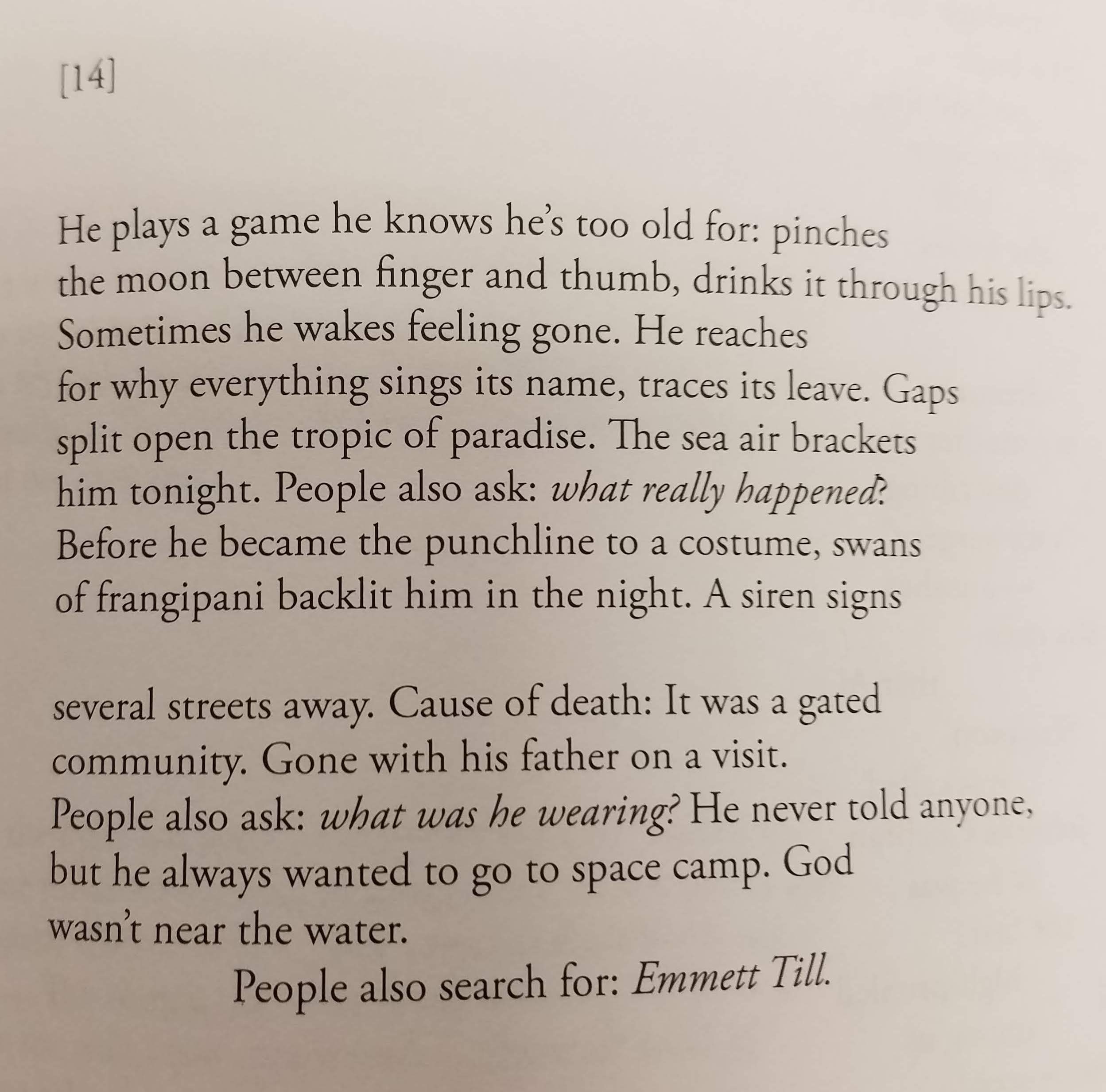
I don't know if that pattern is coded in or is part of Bertram's editing it after the fact.
@patricia_s wrote
I did not see this lawsuit. Didn't he also sue the Martin family? What an incredible scumbag.
This is a lovely riff on what I think Chun is writing about here. On the one hand, she's offering a literal and technical explanation of how RAM works, but she also provides a history of how we came to call RAM "memory" which -- as an allusion to human memory -- actually relies on some unusual and incorrect assumptions about how human memory works. I really like your phrase "talisman for awareness," especially in the context of public memory or memorial.
I don't think it's unsophisticated suggestion at all, and I think this is one really important implication of what Bertram means as an "unimagined programmer." I don't want to speak for her, of course, but I think it's pretty clear that the systems she calls out in her poetry aren't just the literal programming code she uses, but also the broader infoscape -- search engines and algorithms carefully tuned toward advertising more effectively. That is, while the suggested search "What was Trayvon Martin wearing?" is evidence of biased and racially-specific victim blaming, it is also Google trying to help advertisers reach me with their messages. Google is offering that up because people have searched for it, so if I click on that suggestion, Google knows I'm more like the other people who typed that in or clicked on it and, therefore, more likely to respond to the same kind of advertising messages. And this likelihood is what Google can sell.
I realize that that summary of Google's motivation is an oversimplification, but your excellent point about resistance through clicking different got me thinking of the economics of clicks and engagement.
Your point about the spectacle of the suffering of people of color vis a vis who's voices we should privilege also reminds me of Lillian-Yvonne Bertram's response to Kenneth Goldsmith's "Michael Brown's Body". It's an excellent piece, worth quoting at length about how conceptualism operates with a logic that is coextensive with white privilege:
Hi! Just to chime in--I wanted to include the source codes but long story short, didn't do a computer backup. I also changed them all the time--altered words and things, ran it, tweaked the text, changed it, ran it again, and so on. I really appreciate all these thoughts on my work! I also definitely consider Nick M a mentor who has been very important to my learning and practice.
I've been thinking about the title "Counternarratives"?
https://www.goodreads.com/book/show/23308935-counternarratives
In an interview, @lybertram notes one of her favorite books was called Counternarratives by John Keene.
I wonder if this was one of the inspirations. It's interesting to think about how her project responds to this work in addition to Nick's.
Also, @lybertram as long as you're here. Do you remember any of the specific changes you made (or tried out) on @nickm's code?
Thank you for this amazing and deep reflection on Bertram's pieces.
Although I don't have for the moment nothing to add to your analysis of the code, one of the many aspects where I found it very interesting is the fact that you speculated on what the code could have been, and in my personal research I emphasize this type of reading as one that is inherent (and, in a sense, exclusive) of electronic literature. Reading an computer generated text, in my opinion, is not only reading the words and their meaning but also recreating in our minds the source code that generated it. This exercise also informs the meaning of an electronic piece.
Another thing your critique made think of was the fact that in all these pieces, Bertram is in a way reflecting on the very meaning of what a law is, and what are the right boundaries of its application. If we think about freedom in a Rousseauian framework (which, of course, is close to the Kantian version), being free is to only obey to the laws we imposed to ourselves (which is the opposite of Locke's idea of "not being stopped from doing X"). On the other hand, working with texts in a computational environment is working, as the Oulipo school, under the constraints the code imposes (and, sometimes, in the constraints we impose to the code, i.e., working under 256 bytes). One could think about the code as its own legality, its own set of constrains (and, for that reason, its own type of freedom). In this sense, I find very fruitful Bertram's work, and your analysis of it, because it shows how the very structure and material of it also informs the subject on which the work is reflecting on.
@miltonlaufer said:
I certainly agree. And the Feminist A.I. week shows us that reading other blackboxed or unseeable code also involves that kind of work.
To that end, I would like to offer @jeremydouglass' notion of "Implied Code," which he offers in his dissertation as a way that we read interactive fiction, trying to form a picture of what is happening behind the text, and Ville Matias Lmapi's thesis on Twitterbots, which discusses the way we read these kinds of bots by discerning their grammar. (See also Richard Carter's article "Tweeting the Cosmos".) In both instances, like what we are talking about here, readers are trying to model the code to discern the system with which they are engaging.
I look forward to seeing how we can continue to develop these practices in ways that produce repeatable and reliable understandings.
Although maybe there is a value in also speculating on alternative models, the multitude, the infinity, or perhaps just a comparison of divergent ways of getting to the same result. In other words, perhaps there is a productive engagement that could come from offering more personal or individual notions of what the code could be. A particular kind of reader response theory for software and code studies.
@markcmarino
Hi!
Keene's Counternarratives was very much an inspiration.
Something at work in here too, that I was thinking about, was the evolution of "code" (law, like @miltonlaufer points out), from slave codes to coded language for escaped slaves to policing algorithms. That is, in some ways, Zimmerman was "patrolling" (patter roller) his neighborhood and took the black body as being out of place, not where it should have been. He was living a code that sees black bodies in need of policing, which configures (to quote Baraka) the black body as the "ex-slave". Track this forward into the work that Safiya Noble has done, I'm interested in the way anti-blackness has, and continues, to inhabit "codes." That's maybe an alternate rif, but that's what comes to mind when also thinking about Counternarratives and counter codes.
For the changes I might have made to Nick's code: it's unfortunate how many of them are truly lost to time/space. I do know that for something like the Taroko George code, I would set it to produce a single line at a time, for example. What I am so grateful for in this critique/review is that @zachwhalen is getting at sssooo many of the things that were circulating in my brain as I worked on this project. But I played fast and loose with the actual codes, so to speak. I thought I was saving my work with Jupyter's autosave, but I wasn't. I did a lot of "destructive" editing to the codes, constantly overwriting, massaging, and so on. My background is more or less exclusively in creative writing so when I first forayed into this stuff (via rasperry pi) I didn't really know how to organize projects, save code drafts, and the like.
Thank you, all of you, for engaging in my work. This is very meaningful and instructional for me!